Another attempt at a note-taking workflow
In a previous post I mentioned one of the tools I use is Wiki.js. It was a great thing to learn how to set it up but… I was never entirely happy with it:
- It’s somewhat slow on loading.
- Not that customizable yet.
- The update process is a total pain in the ass. They want you to use Docker and this ‘ere server can run it but performance wouldn’t be that nice.
- On mobile I have to depend on the vagaries of whatever browser I’m using (Firefox) so I don’t get that good of an editing interface.
- This is a private repository of knowledge so if it turns out wiki.js has a security issue my wiki is now at risk until I go through the pain of updating again.
So that’s that. I’d been playing with vimwiki since it’s text-based. After a bit of playing I was able to make it work nicely on the gVim instance I run on the Windows 10 desktop and the Ubuntu instance I run in WSL.
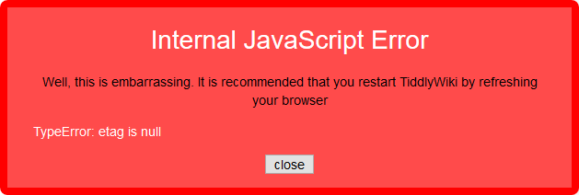
The mobile side of things was immensely helped along by Epsilon Notes, which blows iA Writer completely out of the water. Along the way I tried using Joplin which at first glance seems awesome but then you run into this issue:
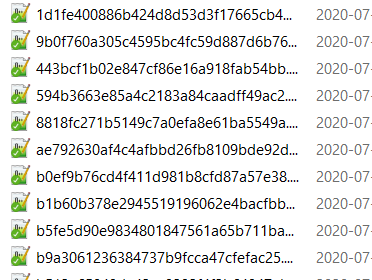
Yes, I get the logic of completely unique filenames but it also means that I’m locked into the app. This is something people have complained about as it defeats all efforts at interoperability. I mean, these are fucken markdown files. And this is an open source app!
Oh right, it also uses its own WebDAV connection to the Nexcloud instance, so slow your roll.
So back to Epsilon. It’s got a few goodies:
- Line numbers
- CommonMark is the default markdown dialect.
- It’s native to Android.
- Let’s you use front matter for tags but doesn’t require it. I personally don’t care for it.
- It sets up its own folder in the device filesystem which you can then sync with Nextcloud.
The workflow
All right, so this is what I have right now
vim/gvim
Assuming there’s already a working Windows gVim instance, a working WSL installation, and a working Nextcloud desktop client:
- Setup vim with vimwiki.
- Configure vimwiki to store its files in a directory being synced by the Nextcloud desktop client. For the sake of simplicity and avoid changing my
.vimrcfile unnecesarily in WSL/ubuntu I symlinked~/vimwikito the appropriate directory in Windows; this way the_vimrcfile in gVim could remain the same. Using either vim instance gets me to the same location. - Create your vimwiki index file:
<Leader>ww, and save it. It should get picked up by Nextcloud.
Nextcloud
Using the web interface or the Android client, mark the vimwiki folder as a favorite so Nextcloud keeps it synced at all times. I don’t think there’s a way to do this in the desktop client yet.
Epsilon Notes
Assuming there’s already a working Nextcloud app
- Install Epsilon from the Play Store.
- Tap the folder icon on the top right and navigate to
/storage/emulated/0/Android/media/com.nextcloud.client/nextcloud/USER@HOST/vimwiki/. If you have multiple Nextcloud accounts on the same app you’ll see all of those listed with a USER@HOST folder each and you can just jump between folders.
Another way of doing this is setting up custom folders but I think doing it this way makes for a simpler configuration. It’d probably be really useful you have multiple vimwikis or multiple Nextcloud accounts though.
Bonus: Servers
I have a couple of boxes that run headless and I also wanted to have my notes available on there. There isn’t a terminal Nextcloud client but I found Rclone. I could have used cadaver but Rclone is designed specifically for cloud file storage:
These instructions worked under my Debian 10 install:
- Install
rcloneandfuse3:sudo aptitude install rclone fuse3. - Configure Rclone with
rclone config. Documentation. - Create an Rclone mount with something like
rclone --vfs-cache-mode writes mount NEXTCLOUD:/vimwiki ~/vimwiki --daemon
Which assumes NEXTCLOUD is what you named the remote configuration, your vimwiki directory lives at $HOME, and you want the connection to remain alive until you decide to stop it manually. The --vfs-cache-mode writes flag will enable some amount of caching. Documentation.
4. At this point you can access your vimwiki as if they were on the local filesystem.
Fucken awesome amirite
SO now we have wiki-like notes that can be edited on desktop, mobile, or server, using whichever editor you prefer. Another bonus: You’re not locked in to anything. I could edit notes on desktop with Notepad++, Sublime Text, or Atom. On mobile you can edit them with whatever text editor you end up with. On a server you can edit them natively with whatever you have at hand.
And in the sad event you don’t have anything you can still access them through the Nextcloud web interface. They even got a markdown editor but I’m not sure what dialect it uses.
The only thing I dont have anymore is a nice clean way to print these notes but this is where pandoc and a print.css file should be useful. If worst comes to worst I can always paste something into LibreOffice and just change the styling that way. Another thing I’ll have to change is how I search for things but since I do have access to the terminal I can always resort to grep if worst comes to worst.
Extras
I did have a few things that led me to try and avoid using web interfaces for this
- The Website Obesity Crisis. Comments on reddit and Hacker News
- The reckless, infinite scope of web browsers
- I tried creating a web browser, and Google blocked me
- Browser bloat has been a problem for a long, long time now.
- The proliferation of browser-based text editors (StackEdit, Dillinger, Editor.md, WordPress) that try to do too much and they end up falling flat on their face cos nothing beats the responsiveness of editing locally.
- The flipside of the above is I can use editors native to each platform. This post was typed on vim, then pasted into WP, for example. This makes for a much, much nicer editing experience specially when doing long-form text or to-do lists.
- Avoiding lock-in. It was a drag to move from one platform to another and paste everything manually, cos all of these tools depend on locking you in.
- Security. My Nextcloud instance is exposed to the Internet but I can always implement more things cos I control the network, the hardware, and the operating system.
- Other people who were also on search of a good editing experience, like this, or this.
- Easy migration of mark-up. I’m trying to use editors that support CommonMark since that way I can always be more or less sure of how something is going to look if I export it elsewhere, and I have the freedom of switching to something else like ReStructured Text or AsciiDoc, which I have considered.
I’m super excited about this. My notes en’t locked in anywhere and they’re all in plain-text, which is the only thing guaranteed to not change in the next 20 years,
Another attempt at a note-taking workflow Read More »